Attacking the ‘Root Causes’ of Improper Payments
Office of Management and Budget (OMB) Deputy Controller Mark Reger recently called for government accountants to take a stronger role in reducing improper payments. “Find out what your agency does about improper payments,” Reger urged at the Association of Government Accountants’ conference held September 21 in Washington, D.C. “In everything you do, start to look for that opportunity to suggest to somebody to improve improper payments.” *
Improper federal payments increased again this past year, rising from $124.7 billion in fiscal year 2014 to $136.7 billion in 2015. Of course, improper payments aren’t just a problem for the U.S. government. Many national governments worldwide, as well as state and provincial governments, struggle to rein in misdirected and fraudulent funds.
Still, the U.S. experience is instructive. In 2015, OMB started examining more closely the “root causes” of improper payments. What strikes us as especially noteworthy is that faulty or incomplete data plays a role in many of the problems.
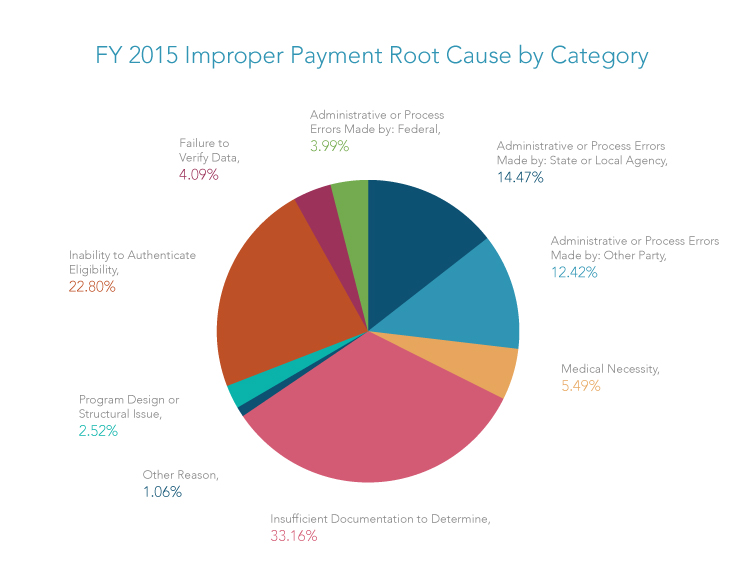
As shown in the chart from the Government Accountability Office (GAO), more than 33 percent of improper payments could be traced to insufficient documentation to verify the accuracy of the payment.** Another 22.8 percent were due to agencies’ inability to authenticate the eligibility of the individuals or entities receiving government funds.
Our own experience helping healthcare agencies oversee healthcare providers is highly consistent with GAO’s conclusions. We have found that the identifying data for as much as 15 percent to 35 percent of providers is lacking in sufficient detail or plagued with inconsistencies to place the providers in a high-risk category meriting further attention.
These shortcomings leave agencies vulnerable to fraud, such as instances where companies use stolen corporate identities, unverifiable addresses, virtual offices, fake business references, or convoluted corporate structures to fraudulently obtain government payments and loans.
Overcoming Barriers: Reducing Risk and Increasing ROI
We have also found that government leaders understand the crucial link between quality data and proper payments. So the question naturally arises: Why aren’t they doing more to ensure data quality that can support more rigorous controls over agency programs, whether it be loan guarantees to small businesses, grants, disaster assistance, social welfare, or healthcare programs?
Two reasons stand out. First, applying stricter controls that require data collection and analysis can slow processes for delivering aid. Government officials want public assistance, whatever its form, to reach its citizens as quickly and efficiently as possible.
Second, agency leaders are uncertain of the return on investment (ROI) they will receive by improving data and analytics. How do you quantify the gain in fraud avoidance?
These are legitimate concerns. With regard to the first concern, we are finally seeing the beginnings of a few progressive agencies taking steps to create more robust provider registration processes. The best of these new systems is so airtight in its registration data requirements that provider applications cannot proceed through the process if even one piece of required data or documentation is missing.
While this more stringent registration process might seem onerous, it actually improves efficiency—for both state regulators and providers—because it eliminates the constant sending of documents back and forth to complete the registration. It also sets a better foundation for proactive fraud risk mitigation by ensuring that the state has all of the required provider information. And if the provider submits incorrect information—whether accidentally or with deceptive intent—the state has more data points to identify discrepancies and uncover improper payments.
Regarding ROI, we have seen government agencies across a wide spectrum of public programs achieve significant returns from their investments in data and analytics.
“Many government decision-makers grossly underestimate the impact and value of external data and analytic assets to address very specific problems and mission challenges,” said Mark Muckerman, Dun & Bradstreet Vice President of State & Local Government Solutions. “The cost of implementing improved data and risk modeling is a fraction of the potential gain in revenue collection or reduction in improper payments and fraud avoidance.”
The precise ROI will depend on a variety of factors, such as an agency’s existing data collection and management infrastructure, project goals, and other variables. Nevertheless, the value of enriched data continues to grow as agencies increase their ability to leverage data with advanced analytics that reduce fraud, waste, and abuse.
“While the multi-million dollar indictments get the most exciting press coverage, the most successful fraudsters are those who systematically bleed a state system with a steady flow of a thousand little cuts for years. As a result, unless they get greedy, stupid or both, detection is nearly impossible without having two essential capabilities: first, the ability to crunch and analyze big data for risk pattern identification; and second, access to the broadest scope of data and intel available, leaving no stone unturned,” Muckerman said.
Improving Program Integrity
So what’s the bottom line? With accurate and reliable data, public sector agencies can better understand the relationships among recipients of government funds. This inevitable evolution to more data-driven risk mitigation processes steadily improves agencies’ ability not only to better uncover fraud, waste, abuse and improper payments, but also to put a tighter screen on the front door and reduce the flow of bad actors entering the system and siphoning off funds and resources from needy citizens.
